SSH with TACACS+
RBFS provides a custom pluggable authentication module that gets invoked by the stock sshd on login. The necessary configurations are pre-installed on RBFS.
RtBrick-PAM, referred to as RTB-PAM helps in landing the TACACS authentication on the appropriate user in the Ubuntu container and helps in providing necessary details for the secure management plane feature.
Once the PAM client requests TACACS for the authentication, with successful authentication TACACS responds with a few RtBrick specific details.
{
rtb-deny-cmds: “clear bgp peer”
priv_lvl : some_level
}
On successful authentication, the RTB-PAM module creates a token (JWT) for the logged-in ssh user.
RTB-PAM Token
Token created by the RTB-PAM module contains the same claims that are defined under the RtBrick Token section, and this token is signed with the secret_jwks.json key.
The scope claim in the rtb-token is derived from the Linux groups that the locally mapped user belongs to.
The deny commands are converted into the claim rtb-deny-cmds. Once the token is created, it is transferred to the environment variable.
setenv RTB_TOKEN = {
"sub": "83692",
"iat": 1516239022,
"exp": 1517239022,
"name": "Admin User",
"preferred_username", "user1",
"scope": "operator tacacs_priv_lvl_8"
"rtb-deny-cmds": "^clear bgp peer"
}
After the RTB-PAM token is created, the CLI prompt appears. If a token is not created for the logged-in user, then the user cannot perform communication with the BD.
SSH User Prompt
After you successfully log into RBFS via SSH, you can see the rtb-token using the shell environment. For example, an SSH prompt may look like the example below.
rtbng@b908f71f63b7:~$ env SSH_CONNECTION=198.51.100.1 33136 198.51.100.44 22 LESSCLOSE=/usr/bin/lesspipe %s %s LANG=C.UTF-8 USER=rtbng PWD=/home/tacacs12 HOME=/home/tacacs12 SSH_CLIENT=198.51.100.1 33136 22 SUDO_USER=rtbng PRIV_LVL=1 SSH_TTY=/dev/pts/1 SUDO_PROMPT=[sudo] password for rtbng: MAIL=/var/mail/rtbng TERM=xterm-256color SHELL=/bin/bash SHLVL=1 LOGNAME=rtbng PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games LESSOPEN=| /usr/bin/lesspipe %s _=/usr/bin/env RTB_TOKEN=eyJhbGciOiJIUzI1NiIsImtpZCI6InJ0YnJpY2siLCJ0eXAiOiJKV1QifQ.eyJleHAiOjE0NTE2MDczMDAsImlhdCI6MTQ1MTYwNjQwMCwiaXNzIjoicnRicmljay1hcGktZ3ciLCJuYW1lIjoiQmhpc2htYSBBY2hhcnlhIiwicHJlZmVycmVkX3VzZXJuYW1lIjoiYmhpc2htYSIsInNjb3BlIjoic3lzdGVtIiwic3ViIjoiOTllOGI0YTEtM2E2Yi00YzI5LWJlZGItN2U3N2NjOTFjZTZiIn0.NOOAcafmHfgx-QFwiC-_VGokbvUwrTOjhfpD9px3hMY
| The users having access to the Linux shell only can see the installed rtb-token in the shell environment. |
User Login Flow
The figure below shows the user login flow.
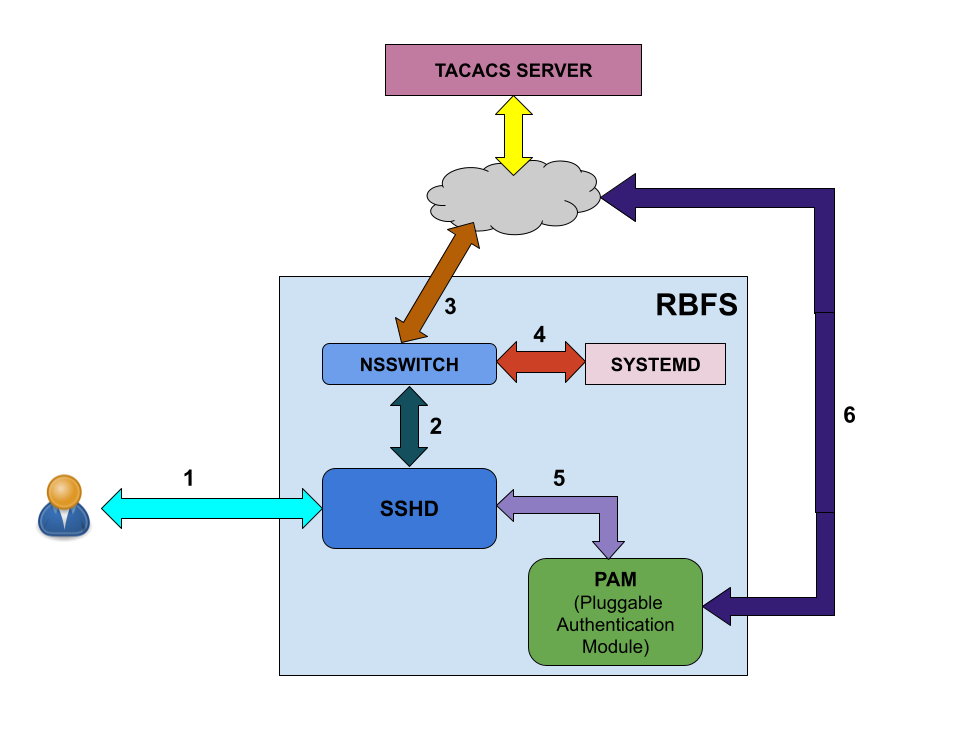
As shown in the figure above, the following steps are involved in the user login flow.
-
User starts to initialize using ssh
-
The SSH daemon (sshd) refers to the Name Service Switch (NSSWITCH) for user lookup
-
NSSWITCH performs a user lookup at the TACACS server
| A user lookup happens at TACACS user database even for the local users, except for the user 'supervisor'. |
-
If the user is not found at TACACS user database, then the user look up happens at the local user database.
-
User authentication is performed by PAM modules
-
PAM communicates to the TACACS server for authentication if it is a TACACS user
Linux pre-configured users and groups
| User Name | Group Name | Privilege |
|---|---|---|
supervisor |
supervisor |
level 15 |
operator |
operator |
level 7-14 |
reader |
reader |
level 0-6 |
In-Band and Out-of-Band TACACS user SSH Login
Configuring TACACS+ for RBFS
To configure TACACS+ server for RBFS, enter the the following commands.
Syntax
Command Arguments
| Attribute | Description |
|---|---|
<ipv4-address> |
IPv4 address of the TACACS+ Server. |
<inband | out-of-band> |
Specifies inband or out-of-band connectivity to the TACACS+ server. |
<inband | out-of-band> port |
Specifies the TACACS+ server’s port. |
<inband | out-of-band> secret-encrypted-text <secret-encrypted-text> |
Specifies the TACACS+ shared secret (encryption) key with a length of 4 to 16419 characters. |
<inband | out-of-band> secret-plain-text <secret-plain-text> |
Specifies the TACACS+ secret (encryption) key in plain text format with a . Specifies the TACACS+ global passkey in plaintext format with a length of 1 to 240 characters. |
|
For TACACS login to work with inband management, inband configuration must be enabled with the following command: set inband-management instance <instance-name> tacacs true |
Example
root@rtbrick: cfg> set system secure-management-status true root@rtbrick: cfg> set system authorization tacacs 192.0.2.130 inband secret-plain-text RtBrick_Little_Secret root@rtbrick: cfg> set inband-management instance inband_mgmt tacacs true
| A TACACS user is not allowed to login without TACACS+ server configuration. |
The example below shows the running configuration after you configure TACACS+.
{
"rtbrick-config:system": {
"authorization": {
"tacacs": [
{
"ipv4-address": "192.0.2.130",
"type": "inband",
"secret-plain-text": "RtBrick_Little_Secret"
}
]
}
}
}
Example: TACACS User Configuration in the TACACS Server
The example below shows the server configurations for rtb-deny-cmds.
To collect debug information, the linux-group="debug_info,rtbrick_confd_sock_access option should be specified.
|
accounting file = /var/log/tac_plus.acct
key = tacacskey
user = bob {
login = cleartext "bob"
member = Network_Operator
}
group = Network_Operator {
default service = permit
service = exec {
priv-lvl = 10
rtb-deny-cmds = "show bgp.*"
linux-groups = "debug_info,rtbrick_confd_sock_access"
}
}
The priv-lvl is a mandatory attribute in the TACACS user configuration. The priv-lvl from 0 to 14 always initiate with "/usr/local/bin/cli" and priv-lvl 15 starts with the Linux shell "/bin/bash".
|
Multiple cmd-regexes can be configured with each regexes separated by semicolon (;).
Example:
rtb-deny-cmds = "show bgp .*;show isis .*"
Troubleshooting NSS User Lookup Issues
To look up the TACACS username with all NSS methods, enter the following command:
ubuntu@rtbrick:~$ sudo getent passwd <tac_user>
To look up the local user within the local user database, enter the following command:
ubuntu@rtbrick:~$ sudo getent -s compat passwd <local_user>
To look up the TACACS user within the TACACS+ server database, enter the following command:
ubuntu@batman:~/development$ sudo getent -s tacplus passwd <tacuser>
If TACACS does not appear to be working correctly, You can enable debug logging by adding the debug=1 parameter to one or more of these files:
/etc/tacplus_servers /etc/tacplus_nss.con