Access Profile Configuration
You must configure an access interface with an access profile name, such as pppoe-dual
and it is also essential to configure the properties and parameters of the access profile itself.
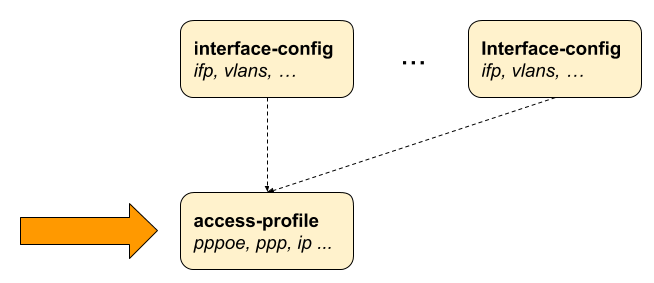
The following image illustrates the access interface configurations and how they are associated with the entire subscriber management configurations.
Configuring the Access Profile
Configuring an access profile involves specifying its name and defining various parameters to control how it handles network traffic and client interactions. The following command and options allow you to configure an access profile.
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Without any option, the command creates an access profile. |
|
Name of the access profile. |
|
Name of the outing instance. Default instance value is 'default'. The instance attribute in the access profile specifies the routing instance for PPPoE subscribers. For IPoE subscribers, the routing instance is determined by the 'gateway-ifl' parameter. |
|
Address-family configuration |
|
Protocol configuration. |
PPPoE with IPv4 and IPv6
The following access profile configuration is a PPPoE access profile named pppoe-dual that supports both IPv4 and IPv6. The instance is marked as default, and the session protection is enabled for PPPoE by setting the value to true, and the VLAN priority is set to 6.
The configuration defines various PPP parameters such as LCP, IPCP, and so on. For LCP (Link Control Protocol), the authentication protocol is specified as PAP_CHAP, indicating that both PAP (Password Authentication Protocol) and CHAP (Challenge Handshake Authentication Protocol) are allowed. The echo-interval, which is the interval in seconds for sending LCP echo requests to check the connection, is specified as 30 seconds. The echo-max-retransmit parameter, which is the maximum number of retransmissions for LCP echo requests before considering the link down, is set to 3. The configuration enables the LCP echo requests by specifying true for the echo-enable parameter.
In the configuration, both the IPCP and IP6CP are enabled by setting their values to true. These protocols are used to configure both the IPv4 and IPv6 settings over PPP. The source IFL (logical interface) for IPCP is specified as 'lo-0/0/0/1'. The RA (Router Advertisement) Configuration is enabled by setting the value to 'true', which allows the router to send RA messages for IPv6 configuration. The interval period for the RA messages is set to 60 seconds. DHCPv6 is enabled by setting the value to true, which allows the device to assign IPv6 addresses to the subscribers through DHCP.
The L2TP tunnel profile is defined as l2tp-default, which allows the encapsulation of PPP sessions over IP networks. Both IPv4 and IPv6 address families are enabled by setting their values to true using the address family configurations. For IPv4, the primary DNS server is specified '198.51.100.1' and the secondary DNS server is specified '198.51.100.4'. For IPv6, the primary DNS server is specified as '2001:db8:0:100::'' and the secondary DNS server is specified '2001:db8:0:104::'.
supervisor@switch: cfg> show config access access-profile pppoe-dual
{
"rtbrick-config:access-profile": {
"profile-name": "pppoe-dual",
"instance": "default",
"protocol": {
"pppoe": {
"enable": "true",
"session-protection": {
"enable": "true"
},
"vlan-priority": 6
},
"ppp": {
"lcp": {
"authentication-protocol": "PAP_CHAP",
"echo-interval": 30,
"echo-max-retransmit": 3,
"echo-enable": "true"
},
"ipcp": {
"enable": "true",
"source-ifl": "lo-0/0/0/1"
},
"ip6cp": {
"enable": "true"
}
},
"ra": {
"enable": "true",
"interval": 60
},
"dhcpv6": {
"enable": "true"
},
"l2tp": {
"tunnel-profile": "l2tp-default"
}
},
"address-family": {
"ipv4": {
"enable": "true",
"primary-dns": "198.51.100.1",
"secondary-dns": "198.51.100.4"
},
"ipv6": {
"enable": "true",
"primary-dns": "2001:db8:0:100::",
"secondary-dns": "2001:db8:0:104::"
}
}
}
}
IPoE with IPv4 and IPv6
The example configuration below sets up an IPoE access profile named 'ipoe-dual' to handle IPoE sessions, which support both IPv4 and IPv6 address families. The router acts as a DHCP server for both protocols, assigning IP addresses and DNS server information to client devices.
The profile name is ipoe-dual. By setting the value to true, this profile enables both DHCP and DHCPv6 protocols. The mode is defined as server for both DHCP and DHCPv6, which allows the router to act as a server for IPv4 and IPv6. The IPv4 address family is configured for the access profile by setting the value to true. For IPv4, proxy ARP is enabled by setting proxy-arp-enable to true.
The IPv4 address family is configured for the access profile by setting the value to ‘true. For IPv4, proxy ARP is enabled by setting proxy-arp-enable to true. This allows the router to respond to ARP requests on behalf of other hosts.
The pool name ipoe indicates the IPv4 address allocation to client devices. The primary DNS server for IPv4 is set to '198.51.100.1', and the secondary DNS server is specified as '198.51.100.4'.
The configuration includes various parameters for IPv6. The IPv6 pool name is ipoe-ia-na, which provides IPv6 addresses to subscribers. The prefix-delegation-pool-name parameter is set as ipoe-ia-pd for IPv6 prefix delegation. The primary and secondary DNS servers for IPv6 are specified as '2001:db8:0:100::' and '2001:db8:0:104::' respectively.
supervisor@switch: cfg> show config access access-profile ipoe-dual
{
"rtbrick-config:access-profile":{
"profile-name":"ipoe",
"protocol":{
"dhcp":{
"enable":"true",
"mode":"server"
},
"dhcpv6":{
"enable":"true",
"mode":"server"
}
},
"address-family":{
"ipv4":{
"enable":"true",
"proxy-arp-enable": "true",
"pool-name":"ipoe",
"primary-dns":"198.51.100.1,
"secondary-dns":"198.51.100.4"
},
"ipv6":{
"enable":"true",
"pool-name":"ipoe-ia-na",
"prefix-delegation-pool-name":"ipoe-ia-pd",
"primary-dns": "2001:db8:0:100::",
"secondary-dns": "2001:db8:0:104::"
}
}
}
}
Unrestricted Proxy-ARP Support for Subscriber IFLs Configuration
This configuration option allows subscriber IFLs to enable unrestricted proxy-ARP, which responds to all ARP requests from subscribers using the MAC address of the corresponding subscriber IFL
Syntax:
Attribute |
Description |
|
Specifies the name of the access profile. |
|
Indicates that the configuration applies to the IPv4 address family. |
|
Enables and controls proxy ARP functionality for the access profile. |
|
Allows the device to respond to ARP requests for any IP address, regardless of whether it belongs to a known subscriber. |
|
Allows the device to respond only to ARP requests for known subscriber IP addresses. |
|
Disables Proxy ARP functionality for the access profile. |
Sample command:
set access access-profile access-profile1 address-family ipv4 proxy-arp any
Example:
supervisor@rtbrick: cfg> show config access access-profile access-profile1
{
"rtbrick-config:access-profile": [
{
"profile-name": "access-profile1",
"protocol": {
"ra": {
"enable": "true"
},
"dhcp": {
"enable": "true",
"mode": "server"
},
"dhcpv6": {
"enable": "true",
"mode": "server"
}
},
"address-family": {
"ipv4": {
"enable": "true",
"pool-name": "pool1",
"proxy-arp": "any"
},
"ipv6": {
"enable": "true",
"pool-name": "pool1",
"prefix-delegation-pool-name": "pool2",
"primary-dns": "1::1"
}
}
}
]
}
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring IPv4
To enable IPv4 support for access protocols like PPP (PPPoE) or DHCP (IPoE), explicitly activate the IPv4 address family in the access profile.
Syntax:
The following table provides the command options/attributes and descriptions.
| Attribute | Description | ||
|---|---|---|---|
|
Enable IPv4. Default: false. |
||
|
The |
||
|
Primary DNS server. |
||
|
The primary DNS and secondary DNS servers configured are used by protocols such as PPP (PPPoE) or DHCP (IPoE) and advertised to the client. |
||
|
Enable (or disable) proxy ARP support for IPoE subscribers. |
||
|
The
|
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring IPv6
To make IPv6 available for access protocols such as PPP (PPPoE) or DHCP (IPoE), you must explicitly enable the IPv6 address family within the access profile.
Syntax:
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Enable IPv6. Default: False. |
|
Local IPv6 pool name. |
|
The |
|
Primary DNS server. |
|
The primary DNS and secondary DNS servers configured are used by protocols such as ICMPv6 router advertisements or DHCPv6 and advertise to the client. |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Enabling IPv6 Router Advertisement
IPv6 Router Advertisement (RA) is a key function within the IPv6 Neighbor Discovery Protocol (NDP). Routers use RA messages to announce their presence and share essential network parameters with IPv6-capable devices. Enabling Router Advertisement is critical for the automatic configuration of IPv6 addresses and related settings on devices supporting IPv6.
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Enable IPv6 router advertisement. Default: False. |
|
IPv6 router advertisements interval in seconds. Sets the interval at which the Router Advertisement messages are sent. Default: 0 ('0' indicates disabled state). |
|
The valid lifetime for the prefix in seconds. Default: 14400. |
|
The preferred lifetime for the prefix in seconds. Default: 1800. |
Configuring DHCPv4
To enable and configure DHCPv4 in the access profile, use the following command. This configuration enables the access profile to process DHCP requests and assign IP addresses to clients.
Syntax:
The following table provides the command options and descriptions.
| Attribute | Description |
|---|---|
|
With any option, the command sets the DHCP mode for the specified access profile. |
|
True or false. Specify true to enable DHCP. Default: False. |
|
This option specifies the DHCP mode for handling DHCP requests. Default: server. Values: server and relay. |
|
Define the duration of IP address leases, in seconds. Default: 300 |
|
Configure global DHCP server. |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring DHCPv6
To configure DHCPv6 in an access profile, use the following command. This configuration activates DHCPv6 functionality, sets prefix lifetimes, and defines the operating mode.
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Enable DHCPv6. Default: False. |
|
This option defines the DHCPv6 mode where the server handles DHCPv6 requests locally and relay/proxy forwards those to the configured servers. The difference between relay and proxy is that proxy can hide the actual DHCPv6 server. Default: server. Values: server and relay. |
|
The duration for which the advertised prefix is valid. This is the total time the prefix remains usable before it needs to be renewed. Set this to the desired lifetime in seconds. Default: 14400. |
|
Set the lifetime for IPv6 prefixes, in seconds. It defines the duration during which the prefix is preferred for use. It should be less than or equal to the lifetime. If set higher than the lifetime, it will be adjusted to match the lifetime. The values for T1 and T2 are 0.5 and 0.8 times the shortest preferred lifetime. Default: 1800. |
|
Configure DHCPv6 server. |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring PPPoE and PPP
The PPPoE protocol must be explicitly enabled in the access profile to allow PPPoE sessions.
PPPoE
The PPPoE configuration allows changing the default behavior of the PPPoE protocol.
Sample command:
set access access-profile pppoe-dual protocol pppoe enable true
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Without any option, the command sets the access protocol. |
|
Enable PPPoE. Default: False. |
|
Maximum outstanding PPPoE sessions. Default: 64 Range: 1 - 65535. |
|
PPPoE session protection. When PPPoE session protection is enabled, any short-lived or failed sessions are logged. By default, a session that does not remain established for at least 60 seconds (min-uptime) is classified as a failed or short-lived session. Such failures trigger a block on new sessions for this IFP, VLAN, and MAC for one second (min-lockout) by default. With each subsequent failed session, the lockout duration increases exponentially until it reaches a maximum of 300 seconds (max-lockout). If no failed sessions occur for 900 seconds, the lockout interval is reset (currently, not configurable). PPPoE session protection also logs the last subscriber ID and terminates the session with a code that indicates the reason for the failure. |
| Attribute | Description |
|---|---|
|
Without any option, the command sets session protection for the access profile. |
|
Enables PPPoE session protection. Default: false. |
|
Session protection minimum lockout time (in seconds). Default: 1. |
|
Session protection maximum lockout time (in seconds). Default: 300. |
|
Session with an uptime less than this will trigger protection (in seconds). Default: 60. |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring PPP LCP
The PPP Link Control Protocol (LCP) configuration allows changing the default behavior of the LCP protocol.
Syntax:
The following table provides the command options and description.
| Attribute | Description |
|---|---|
|
This option allows you to specify the authentication protocol used during the LCP negotiation phase. By default, PPP authentication is set to |
|
By default, RBFS responds to LCP echo requests but does not initiate them unless |
|
LCP echo request interval in seconds. Default: 30, Range: 1 - 255. |
|
LCP echo request retransmissions. Default: 3, Range: 1 - 255. |
|
Negotiate MRU. Default: true. |
|
Maximum local MRU (peer MTU). Default: 1492, Range: 1280 - 1500. |
|
Maximum local MTU (peer MRU). Default: 1492, Range: 1280 - 1500. |
|
This is used during the PPP connection process to detect and prevent loops in the network. It is achieved through the negotiation and validation of 'magic numbers'. Magic numbers are unique values used by both ends of a PPP connection to ensure that the data sent is not simply being looped back from the other end. By default, the negotiation and validation of magic numbers are enabled, providing protection against looping connections. You can disable loop detection by setting |
|
The LCP request retransmission interval. Default: 5, Range: 1 - 255. |
|
The LCP requests retransmission before the session is terminated if no response is received. Default: 3, Range: 1 - 255. |
|
The option |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring PPP IPCP
To configure IPv4 over PPPoE, explicitly enable both the address-family IPv4 and the PPP IPCP protocol in the access profile. The source-ifl is a mandatory option that specifies the logical interface from which the local IPv4 address will be derived.
Syntax:
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Enable IPCP. Default: False. |
|
IPCP passive mode. Default: False. |
|
This setting is required and should be set to obtain the local IPv4 address from a specific logical interface. It should be configured to use the loopback interface of the corresponding routing instance. If a |
|
The IPCP request retransmission interval. Default: 5, Range: 1 - 255. |
|
The IPCP requests retransmission before the session is terminated if no response is received. Default: 8 Range: 1 - 255. |
|
The option config-nak-max defines the maximum PPP IPCP configuration reject/nak messages that can be sent or received before the session is terminated. Default: 8, Range: 1 - 255. |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Configuring PPP IP6CP
To enable IPv6 over PPPoE, you must explicitly configure both the IPv6 address family and the PPP IPv6 Control Protocol (IP6CP).
The following command demonstrates how to enable PPP IP6CP in the pppoe-dual access profile.
The following table provides the command options/attributes and descriptions.
| Attribute | Description |
|---|---|
|
Enable IP6CP. Default: false. |
|
IP6CP passive mode. Default: false. |
|
This option sets the interval, in seconds, between retransmissions, for IP6CP requests. Default: 5 Range: 1 - 255. |
|
This option sets the maximum number of retransmission attempts. The IP6CP requests retransmission before the session is terminated if no response is received. Default: 8, Range: 1 - 255. |
|
The option defines the maximum PPP IP6CP configuration |
 To access the RESTCONF API that corresponds to this CLI, click
here.
To access the RESTCONF API that corresponds to this CLI, click
here.
Retention Timer for Subscriber Termination History Configuration
You can configure a retention period (in hours) for storing the termination history of access subscribers after they have been disconnected.
Syntax:
| Option | Description |
|---|---|
|
Specify the period of time (in hours). Range: 0 - 720. If '0' is specified, the data is not retained. |
Example:
set access terminate-history-timeout 10
{
"rtbrick-config:access": {
"terminate-history-timeout": 10
}
}