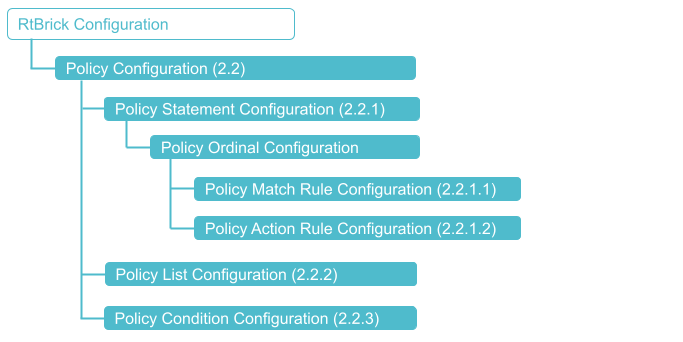
Policy Configuration
Configuration Syntax and Commands
The following sections describe the policy configuration syntax and commands.
Configuring Policy Statements
Syntax:
set policy statement <policy-name> ordinal <number> <attribute> <value>
| Attribute | Description |
|---|---|
<policy-name> |
Name of the policy statement. Policy names can contain alphanumeric characters and underscore character. They must not include special characters like hyphen. For example, BGP-EXPORT is not supported, whereas BGP_EXPORT is supported. A valid name cannot start with a number but it can contain numbers and underscore (_) in the string. The length of the names should not exceed 64 characters. |
<number> |
Specifies the ordinal number. |
description <text> |
Description of the ordinal. |
match <…> |
Match configuration hierarchy. Please refer to section 2.2.1.1 for the match rule configuration. |
match-logic <value> |
Specifies the match logic. Supported values are |
action <…> |
Action configuration hierarchy. Please refer to section 2.2.1.2 for the action rule configuration. |
condition <condition-name> |
Optionally, apply a policy condition. Please refer to section 2.2.3 for the policy condition configuration. |
Configuring Match Rules
Syntax:
set policy statement <policy-name> ordinal <number> match rule <number> <attribute> <value>
| Attribute | Description |
|---|---|
rule <number> |
Specifies the match rule number. |
type <attribute-type> |
Specifies the attribute type. Please refer to section 2.2.1.1.1 for supported attribute types. |
match-type <match-type> |
Specifies the match type. Please refer to section 2.2.1.1.1 for supported match types per attribute, and to section 2.2.1.1.2 for descriptions of the match types. |
value <value> |
Attribute value. This is the actual value of the attribute to match, for example an IP prefix, a metric, or a community. |
value-type <value-type> |
Attribute value type. Supported types are |
Attribute and Match Types
| Attribute Type | Match Types Supported |
|---|---|
ipv4-prefix |
regex |
ipv6-prefix |
regex |
route-distinguisher |
regex |
community |
regex |
extended-community |
regex |
large-community |
regex |
as-path |
regex |
cluster-list |
regex |
source |
regex |
sub-source |
regex |
originator-identifier |
regex |
peer-router-id |
regex |
ipv4-nexthop |
regex |
ipv6-nexthop |
regex |
label |
regex |
peer-ipv4 |
regex |
peer-ipv6 |
regex |
sid |
regex |
sid-flag |
regex |
external |
exact |
Match Types
| Match Types | Description |
|---|---|
regex |
An attribute can be matched using a standard Linux egrep regular expression. Example: "label": "label-op:push,label:206,bos:1" In this example, the label is a 64bit number, which has label value, bos, and operation encoding. A |
exact |
Value configured in the command must be same as application attribute value |
exists |
This is applicable only for array type attribute; an exist match is the one where value configured in the command must exist in the application attribute value which is an array. |
less |
The application attribute value must be less than the value configured in the command |
less-or-exact |
The application attribute value must be less than or exact value configured in the command |
greater |
The application attribute value must be greater than the value configured in the command |
greater-or-exact |
The application attribute value must be greater than or exact value configured in the command |
greater-longer |
The route shares the same most-significant bits (described by prefix-length), and prefix-length is greater than the route’s prefix length |
greater-or-longer |
The route shares the same most-significant bits (described by prefix-length), and prefix-length is equal to or greater than the route’s prefix length. |
longer |
The route address shares the same most-significant bits as the match prefix (destination-prefix or source-prefix). The number of significant bits is described by the prefix-length component of the match prefix. |
or-longer |
The route address shares the same most-significant bits as the match prefix (destination-prefix or the source-prefix). The number of significant bits is described by the prefix-length component of the match prefix. |
prefix-length-exact |
The application attribute value whose prefix length must be lesser than or exact the value configured in the command |
prefix-length-greater |
The application attribute value whose prefix length must be greater than the value configured in the command |
prefix-length-greater-or-exact |
The application attribute value whose prefix length must be greater than or exact value configured in the command |
Configuring Action Rules
Syntax:
set policy statement <policy-name> ordinal <number> action rule <number> <attribute> <value>
| Attribute | Description |
|---|---|
rule <number> |
Specifies the action rule number. |
operation <operation-type> |
Specifies the operation type. Please refer to section 2.2.1.2.1 for supported operations, and to section 2.2.1.2.2 for operations per attribute. |
type <attribute-type> |
Specifies the attribute type. Please refer to section 2.2.1.2.2 for supported attribute types. |
value <value> |
Specifies the operation value. |
Operation Types
| Operation Type | Description |
|---|---|
add |
The application attribute value will be added with the value configured in the command |
append |
The application attribute value will be appended with the value configured in the command |
delete-attribute |
Deletes the attribute from the route/BDS object, that is, clearing all the info for that specific attribute in the object |
divide |
The application attribute value will be divided with the value configured in the command |
goto-next-ordinal |
If next term exists, then next term is executed and the policy result is decided based on the result of the execution |
multiply |
The application attribute value will be multiplied with the value configured in the command |
overwrite |
The application attribute value will be overwritten with the value configured in the command |
prepend |
The application attribute value will be prefixed with the value configured in the command |
return-deny |
Stops policy execution and returns result as |
return-permit |
Stops policy execution and return result as permit (resulting route/BDS object to be permitted) |
subtract |
The application attribute value will be subtracted with the value configured in the command. If the result of the subtraction results in a number less than 0, the value "0" is used. |
Attribute Types and Supported Operations
| Attribute Type | Operation Types Supported |
|---|---|
ipv4-prefix |
overwrite |
ipv6-prefix |
overwrite |
route-distinguisher |
overwrite |
community |
append |
extended-community |
append |
large-community |
append |
as-path |
append |
cluster-list |
append |
source |
overwrite |
sub-source |
overwrite |
originator-identifier |
overwrite |
peer-router-id |
overwrite |
ipv4-nexthop |
overwrite |
ipv6-nexthop |
overwrite |
label |
overwrite |
peer-ipv4 |
overwrite |
peer-ipv6 |
overwrite |
sid |
overwrite |
sid-flag |
overwrite |
external |
overwrite |
Example: Policy statement configuration
{
"rtbrick-config:policy": {
"statement": [
{
"name": "EXPORT_POLICY1",
"ordinal": [
{
"ordinal": 10,
"description": "Add BGP community to direct routes",
"match-logic": "and",
"match": {
"rule": [
{
"rule": 1,
"type": "ipv6-prefix",
"value-type": "discrete",
"match-type": "or-longer",
"value": "2001:db8:0:60::/32"
},
{
"rule": 2,
"type": "source",
"value-type": "discrete",
"match-type": "exact",
"value": "direct"
}
]
},
"action": {
"rule": [
{
"rule": 1,
"type": "community",
"operation": "append",
"value": "100:1"
},
{
"rule": 2,
"operation": "return-permit"
}
]
}
},
{
"ordinal": 20,
"description": "Allow any other route",
"action": {
"rule": [
{
"rule": 1,
"operation": "return-permit"
}
]
}
}
]
}
]
}
}
Configuring Policy Lists
Syntax:
set policy list <list-name> <list-type> ordinal <ordinal-number> value <value>
| Attribute | Description |
|---|---|
<list-name> |
Name of the policy list |
<list-type> |
Type of the policy list. The following types of lists are supported: * as-path |
<ordinal-number> |
The number of the list entry. |
<value> |
The value of the list entry, for example an IP prefix, or a community. |
Example: Policy list configuration
{
"rtbrick-config:policy": {
"list": [
{
"name": "PREFIX_LIST1",
"type": "ipv6-prefix",
"ordinal": [
{
"ordinal": 1,
"value": "2001:db8:0:10::/32"
},
{
"ordinal": 2,
"value": "2001:db8:0:25::/32"
},
{
"ordinal": 3,
"value": "2001:db8:0:30::/32"
}
]
}
]
}
}
Configuring Policy Conditions
Policy conditions refer to certain states of the system represented in BDS tables. You need to specify the table, the daemon (BD) that needs to resolve the condition, and if applicable, the attributes used to define the condition.
There are two types of conditions:
-
Match on certain attributes in BDS table objects.
-
Match on the number of objects in a BDS table.
Configuring Table Match
Syntax:
set policy condition <condition-name> table <attribute> <value>
| Attribute | Description |
|---|---|
<condition-name> |
Name of the policy condition |
name <table-name> |
Name of the BDS table |
bd <bd-name> |
Name of the BD which resolves the condition. Currently supported BDs are: ifmd, ribd, mribd, pppoed, subscriberd, ipoed, l2tpd, pimd, igmp.iod, isis.iod, ospf.appd ospf.iod |
count <number> |
Optionally, match on the number of objects in a table |
match <type> |
Type of match for an object count. Supported match types are: |
Configuring Attribute Match
You can configure attributes to define a condition. The attributes refer to objects in the table configured in the section above. Please note:
-
You can match on multiple attributes.
-
In order to identify matching objects, you need to specify all attributes which are primary keys in the table.
-
Attribute configuration is not required for conditions matching on the number of table objects using the
countoption.
Syntax:
set policy condition <condition-name> attribute <name> <attribute> <value>
| Attribute | Description |
|---|---|
<condition-name> |
Name of the policy condition |
attribute <name> |
Name of the attribute in the BDS table |
value <value> |
Value of the attribute to match |
match <type> |
Type of the match. Supported match types are: |
Example: Policy condition configuration
{
"rtbrick-config:policy": {
"condition": [
{
"condition_name": "precheck",
"table": {
"name": "global.instance",
"bd": "bgp.iod.1"
},
"attribute": [
{
"name": "instance_name",
"match": "equal",
"value": "default"
}
]
}
]
}
}
Attaching Policies
Once a policy has been created, they need to be applied to an application like a routing protocol to take effect.
BGP Attachment Points
-
Instance import/export
-
BGP peer group import/export
-
BGP redistribution
For attaching policies to the BGP protocol, please refer to the RBFS BGP User Guide.
Sample Configurations
Example 1: BGP export policy referencing a policy list
supervisor@leaf1: cfg> show config policy
{
"rtbrick-config:policy": {
"list": [
{
"name": "PREFIX_LIST2",
"type": "ipv6-prefix",
"ordinal": [
{
"ordinal": 1,
"value": "2001:db8:0:60::/32"
},
{
"ordinal": 2,
"value": "2001:db8:0:80::/64"
},
{
"ordinal": 3,
"value": "2001:db8:0:110::/64 "
}
]
}
],
"statement": [
{
"name": "EXPORT_POLICY2",
"ordinal": [
{
"ordinal": 10,
"description": "Add community to direct routes",
"match": {
"rule": [
{
"rule": 1,
"type": "source",
"value-type": "discrete",
"match-type": "exact",
"value": "direct"
}
]
},
"action": {
"rule": [
{
"rule": 1,
"type": "community",
"operation": "append",
"value": "100:1"
},
{
"rule": 2,
"operation": "return-permit"
}
]
}
},
{
"ordinal": 20,
"description": "Allow list of routes",
"match": {
"rule": [
{
"rule": 1,
"type": "ipv6-prefix",
"value-type": "list",
"match-type": "or-longer",
"value": "PREFIX_LIST2"
}
]
},
"action": {
"rule": [
{
"rule": 1,
"operation": "return-permit"
}
]
}
},
{
"ordinal": 30,
"description": "Deny any other route",
"action": {
"rule": [
{
"rule": 1,
"operation": "return-deny"
}
]
}
}
]
}
]
}
}
supervisor@leaf1: cfg> show config instance default protocol bgp peer-group spine address-family ipv6 unicast
{
"rtbrick-config:address-family": [
{
"afi": "ipv6",
"safi": "unicast",
"policy": {
"export": "EXPORT_POLICY2"
}
}
]
}
Example 2: IGMP filter policy
supervisor@leaf1: cfg> show config policy
{
"rtbrick-config:policy": {
"statement": [
{
"name": "IGMP_FILTER",
"ordinal": [
{
"ordinal": 1,
"description": "IGMP group filter",
"match-logic": "or",
"match": {
"rule": [
{
"rule": 1,
"type": "ipv4-mcast-group",
"value-type": "discrete",
"match-type": "or-longer",
"value": "198.51.100.30/24"
},
{
"rule": 2,
"type": "ipv4-mcast-group",
"value-type": "discrete",
"match-type": "or-longer",
"value": "198.51.100.40/24"
}
]
},
"action": {
"rule": [
{
"rule": 1,
"operation": "return-permit"
}
]
}
}
]
}
]
}
}
supervisor@leaf1: cfg> show config multicast-options igmp
{
"rtbrick-config:igmp": {
"interface-profile": [
{
"profile-name": "PROFILE1",
"filter-policy": "IGMP_FILTER"
}
]
}
}